As connectivity collapses, users turn to complex tools and unregulated markets—facing fraud, surveillance, and serious security risks
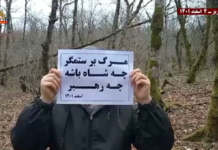
Amid a widespread internet blackout in Iran, the market for VPN services and connection configurations has surged dramatically. What has emerged is a chaotic and high-risk ecosystem where users struggle not only to regain access to the global internet, but also to navigate growing threats of fraud, surveillance, and data exploitation.
Prices for VPN configurations have skyrocketed, reportedly reaching between 500,000 and one million tomans per gigabyte. Yet the issue is no longer simply connecting to the internet—it is about how that connection is established, through which pathway, and at what cost to user security and privacy.
A Fragmented and Restricted Internet
Recent network monitoring data suggests that fewer than 2% of people in Iran currently have access to the global internet. A significant portion of this limited access is reportedly restricted to users with specially authorized SIM cards. Statements by government officials have further reinforced this reality, indicating that access has been selectively granted to individuals deemed capable of “effectively transmitting information.”
This controlled access underscores the severity of restrictions and highlights the state’s effort to tightly regulate information flows during periods of unrest or instability.
The Evolution of VPN Technology Under Censorship
The tools currently enabling connectivity in Iran differ significantly from traditional VPNs. Instead of relying on a single connection method, modern circumvention tools employ multi-layered and adaptive techniques designed to evade detection and blocking.
Among the most widely used methods in recent weeks are DNS tunneling (via tools such as DNSTT and NoizDNS), QUIC packet tunneling using Slipstream techniques, HTTPS-based proxying with NaiveProxy, SSH tunneling, and DNS-over-HTTPS (DoH) encryption. These approaches allow traffic to be rerouted dynamically, ensuring that if one pathway is blocked, alternative routes remain available.
A defining feature of these tools is their flexibility. Some services chain multiple techniques together—for example, layering SSH over DNS tunneling or HTTPS proxies—to increase encryption depth and reduce the likelihood of DNS leaks. In a network environment where filtering operates across multiple layers, such hybrid approaches have proven more resilient than conventional VPNs.
However, these solutions often require technical expertise. As a result, a parallel market has emerged offering simplified “configurations” tailored for less experienced users. In this model, providers preconfigure connection settings, and users simply import a file or key to establish access.
Trust, Surveillance, and Hidden Risks
This convenience comes at a cost. Users must place significant trust in configuration providers, who may have the ability to monitor or log user activity. Even when traffic is encrypted via HTTPS, providers can still identify which services users access, if not the full content of their communications.
Security risks extend beyond surveillance. Misconfigured or malicious setups can expose sensitive data, route traffic through compromised servers, or even leak portions of activity outside encrypted channels. Unlike malware, these risks are structural—embedded in how the connection itself is designed.
Fraud in a Booming Black Market
The surge in demand has also led to a sharp rise in scams. Numerous Telegram channels now advertise “guaranteed VPNs” or “uninterrupted configurations,” often deceiving users.
Fraud typically takes two forms: either no service is delivered after payment, or the service is cut off prematurely—well before the purchased data is used. Many users report buying multi-gigabyte plans that stop functioning after minimal usage, only to be pressured into paying again for supposedly more “stable” access.
Identity Exposure Begins at Purchase
One of the most overlooked risks arises at the point of purchase. When users pay through official banking gateways using real identities, they may unknowingly expose personal and financial information before even using the service.
Given that many VPN providers rely on such payment methods, users can effectively become identifiable from the outset—posing a serious concern for those seeking anonymity in a highly monitored environment.
Can VPN Users Be Identified?
Recent reports of police text messages warning users about accessing the international internet—and threatening SIM card deactivation or legal action—have raised concerns about whether authorities can identify VPN users.
While no definitive public evidence confirms systematic identification, technical analysis suggests it is plausible. With over 98% of users offline, the volume of internet traffic is extremely limited, making anomalous patterns easier to detect.
Network monitoring systems can employ Deep Packet Inspection (DPI) and traffic fingerprinting to identify VPN usage. Even when protocols are obfuscated, behavioral patterns—such as packet size, timing intervals, traffic flow symmetry, and connection persistence—can reveal the presence of encrypted tunneling.
In some cases, the structure and rhythm of data exchanges alone can provide enough indicators for detection.
Misconceptions About Security
A common misconception is that using a reputable application alone guarantees safety. In reality, the configuration itself is a critical component of security. It determines routing paths, server endpoints, DNS handling, and certificate validation.
An untrusted configuration can redirect traffic through insecure servers, enable logging or interception, or allow sensitive data to bypass encryption entirely. In effect, the configuration defines the actual security of the connection—not just the app.
A High-Stakes Digital Environment
As Iran’s internet restrictions deepen, users are forced into an increasingly complex and dangerous digital landscape. Access to information now depends not only on technical ingenuity but also on navigating a largely unregulated and exploitative market.
In such conditions, the line between connectivity and vulnerability continues to blur—turning the simple act of going online into a calculated risk.